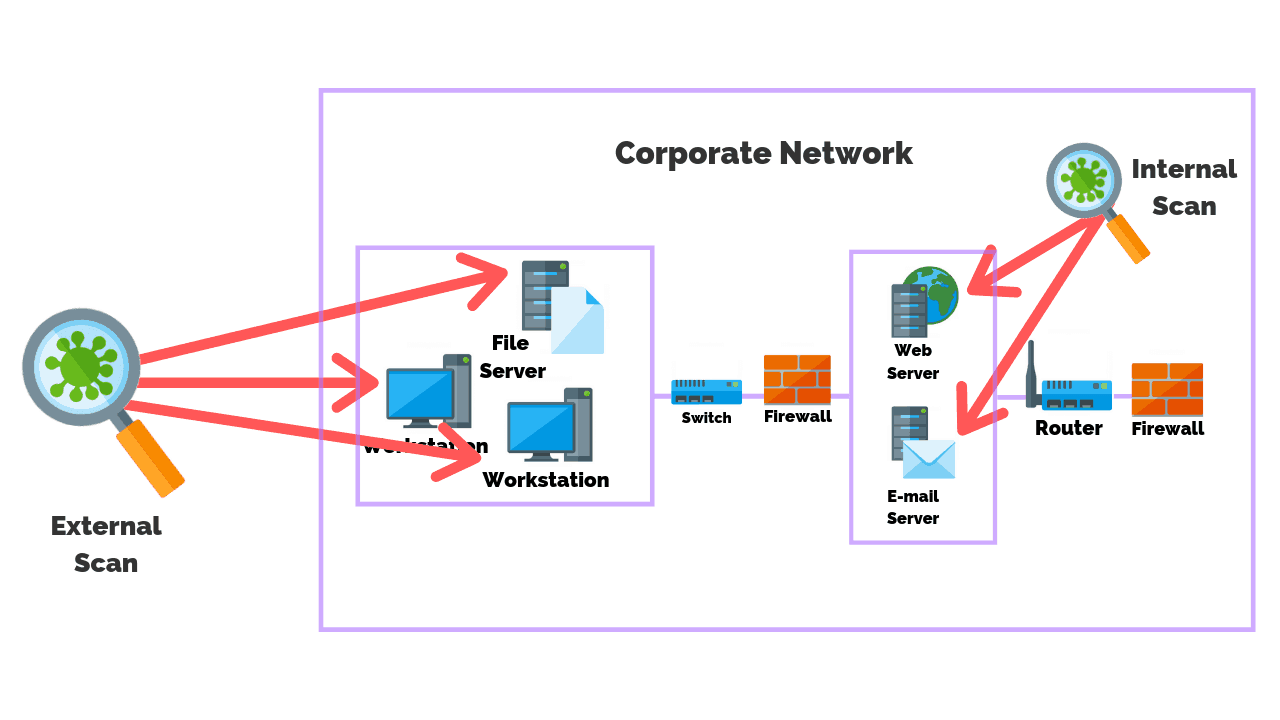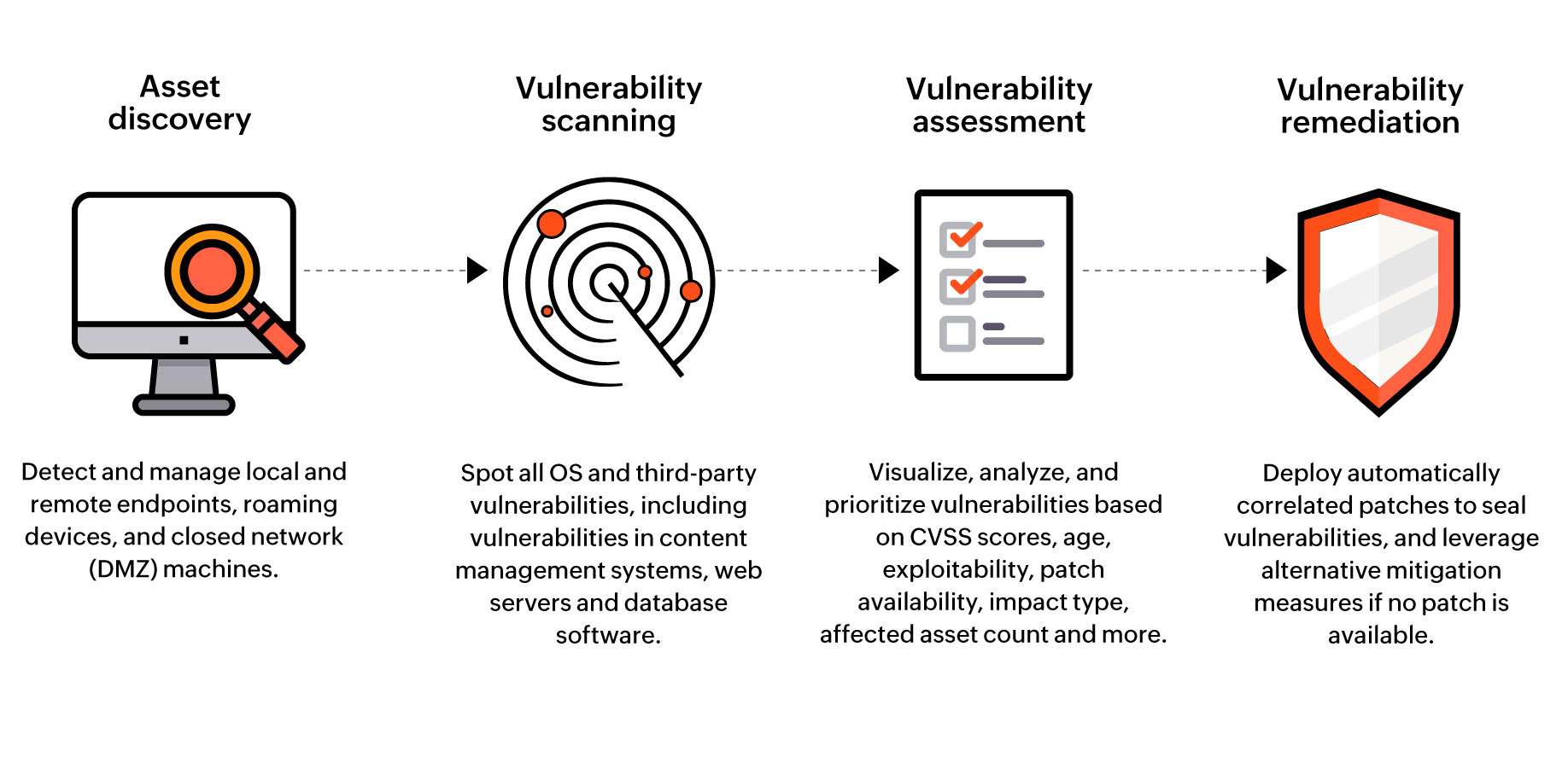
Vulnerability Assessment Tool | Security Vulnerability Assessment - ManageEngine Vulnerability Manager Plus

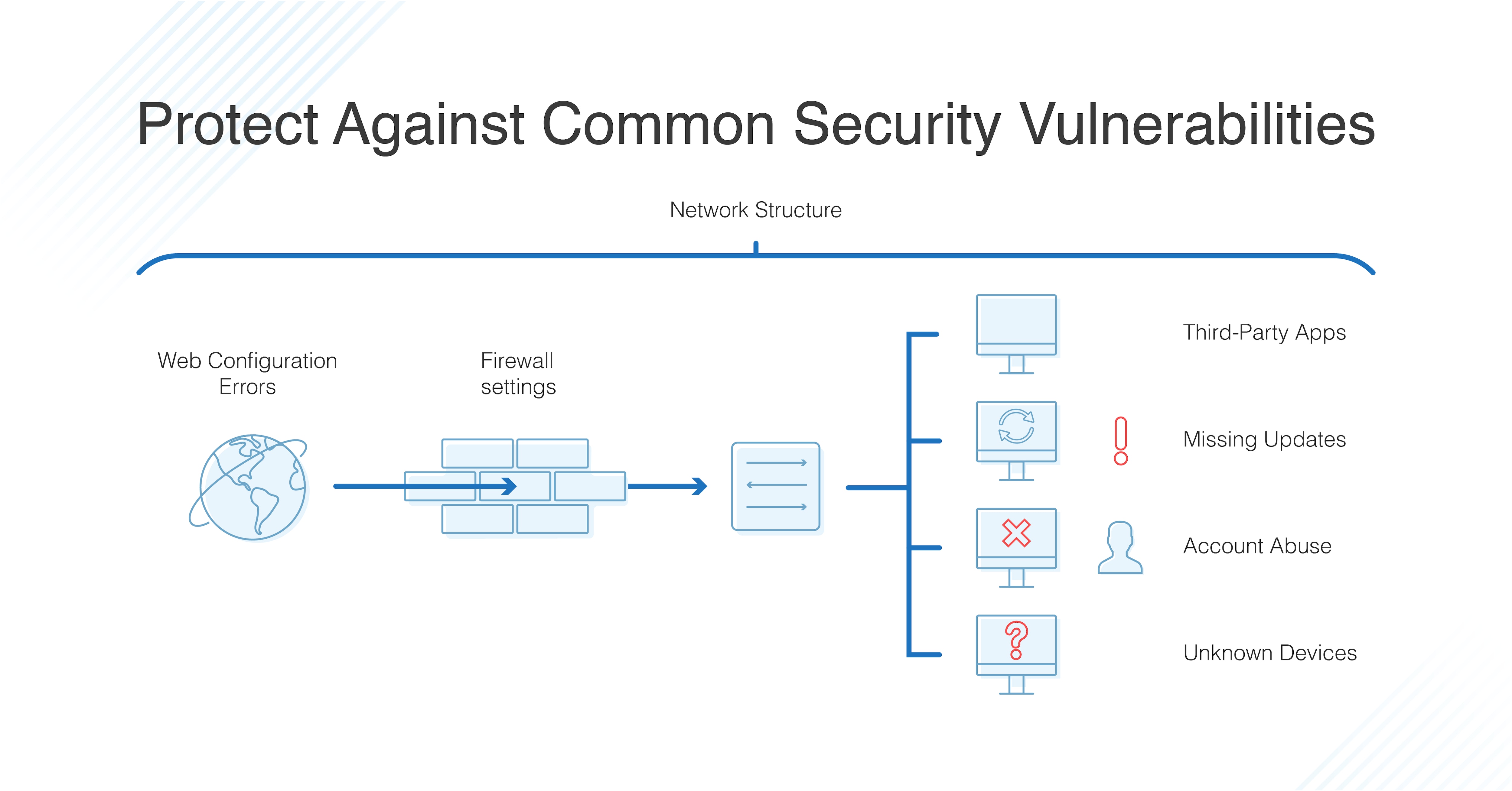
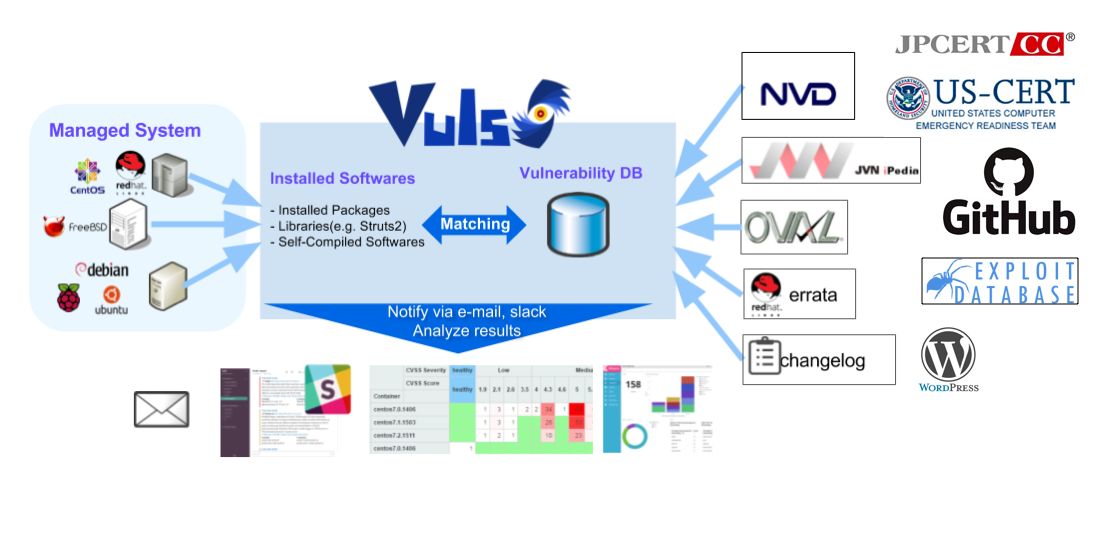
A survey on vulnerability assessment tools and databases for cloud-based web applications - ScienceDirect

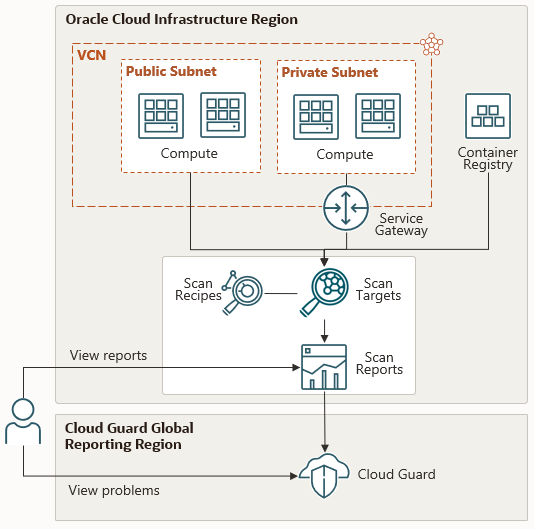
Guard against security vulnerabilities in your software supply chain with Container Registry vulnerability scanning | Google Cloud Blog